Is The Software Supply Chain (The Most Valuable But Least Defended Infrastructure) Under Attack in 2026?
When the password manager gets breached, what's left to trust? A deep dive into what looks like a coordinated, months-long campaign against the AI developer ecosystem and why we're at the beginning, not the end.
The past few weeks in tech haven't been a series of unfortunate security incidents. It seems to be a coordinated campaign, planned months ago, and executed in sequence by multiple groups who knew what the others were doing.
Everything can likely be traced down to Trivy (a security scanner). The irony of using a security tool as a weapon was intentional. From Trivy, they got into LiteLLM, which holds API keys for every major AI provider simultaneously. From LiteLLM, they got into Mercor, whose clients include major players like Anthropic, OpenAI, and Meta.
Lapsus$ (the same group that previously breached Microsoft, Nvidia, Uber, and Okta) had prior knowledge before the attacks went public, which was documented in their Telegram. They knew before the first incident.
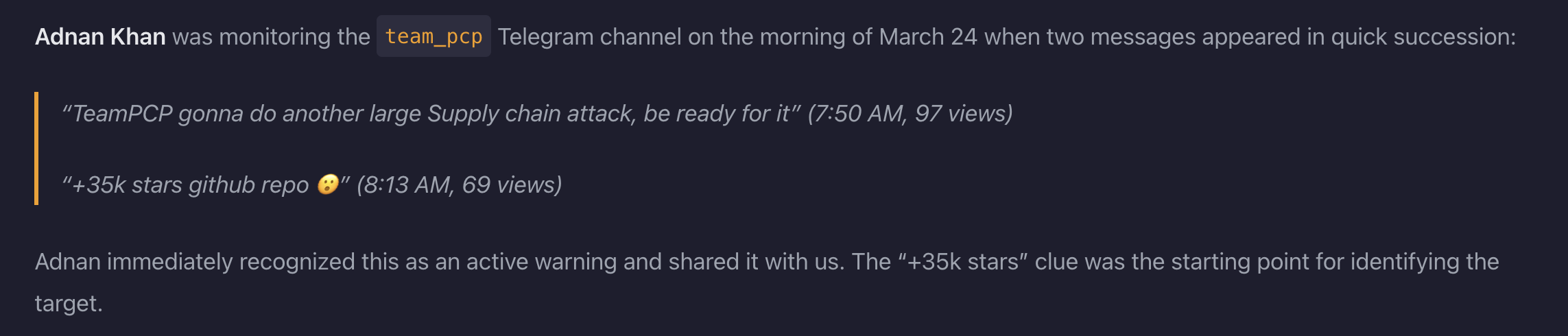
Then the Vercel breach. A North Korean state actor hit the Axios npm package, which is used by 100 million developers weekly. Then Anthropic's most dangerous model was accessed by unauthorized users on the day it was announced.
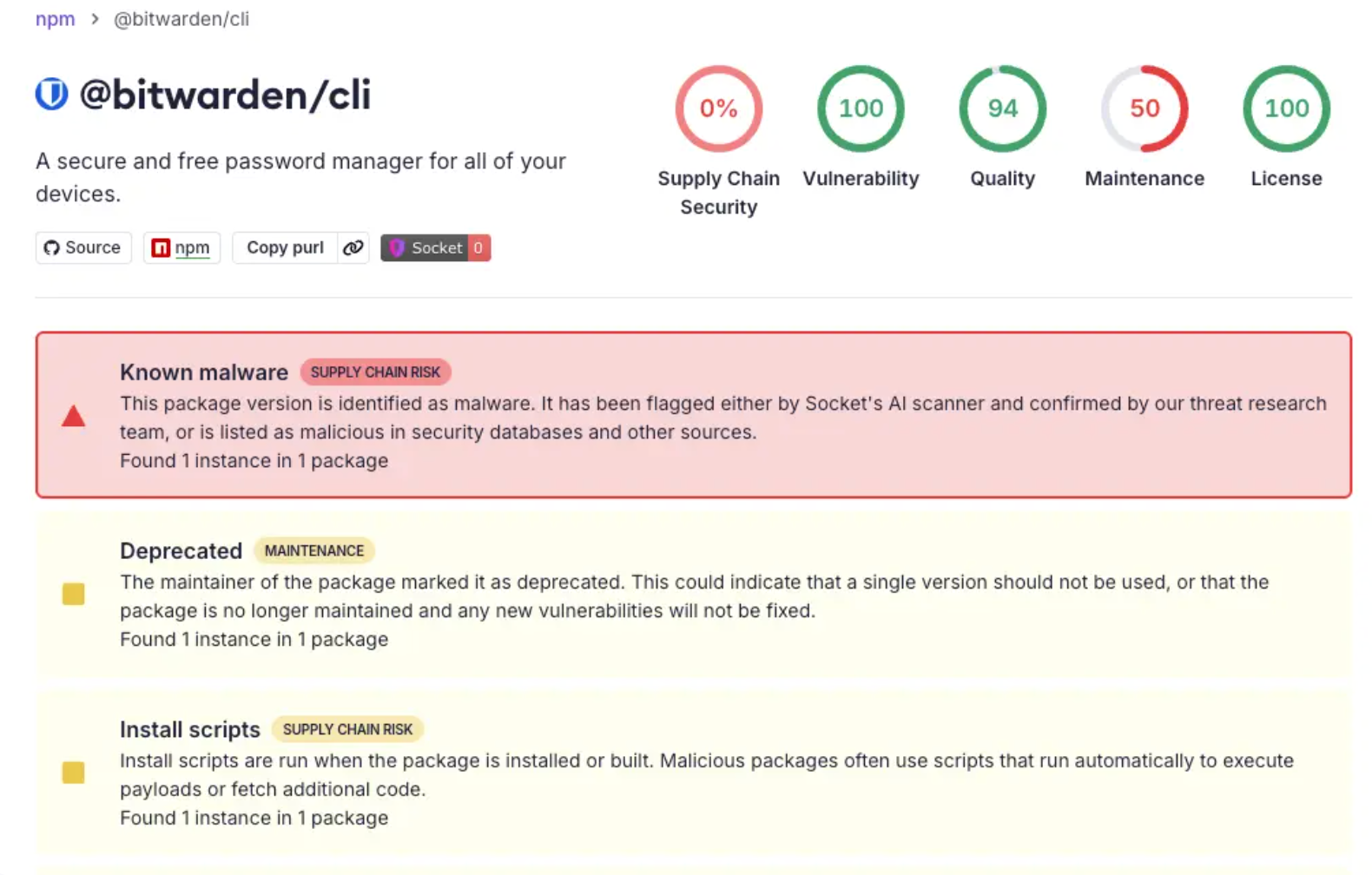
And just a few days ago, Bitwarden CLI, used by 10 million people and 50,000 businesses, was compromised through the same supply chain vector. The malware this time had "LongLiveTheResistanceAgainstMachines" embedded in it, targeting Claude and MCP configuration files specifically.
This does not feel/look random. It looks very much targeted. The AI developer ecosystem is the most valuable, least defended infrastructure on the internet right now and multiple sophisticated adversaries have all figured that out .
If you're building with AI or have built anything with AI, you need to review every dependency, OAuth grant, and CI/CD credential. Rotate anything you haven't rotated recently
For the past few years, since the arrival of AI, we optimized for speed, deferred security, and now the bill has arrived faster than anyone expected.
And it gets worse.
Bitwarden (a password manager) - the thing we trust to protect everything else we have built our system on got breached.
So I'll ask the question nobody seems to want to ask out loud: if the tools we built to keep us safe are now the attack surface, how safe are we, really?
Is this the end of a coordinated campaign? Or is this the beginning of one? Because if you look at the malware, the Dune references, the "LongLiveTheResistanceAgainstMachines" commit messages, the Butlerian Jihad strings targeting Claude and MCP configurations specifically, someone out there isn't just stealing credentials for money. Someone has declared a philosophy. A war against machines, against AI, and against the ecosystem we're all building inside.
Whether that's a lone ideologue, a splinter group, or a state actor using ideology as cover, I don't know. Nobody does yet.
What I do know is this: the attacks started with tools that scan for vulnerabilities. They ended with access to the most dangerous AI model ever built. And they worked because we built an entire ecosystem on speed, convenience, and implicit trust, and nobody audited the chain.
We are not at the end of this. We are at the beginning of understanding how exposed we already are.
Related Blogs and Articles
Engineering Hiring Intelligence. Fortnightly.
The hiring signals, research findings, and founder insights that actually matter - delivered to your inbox every two weeks.
You Can Unsubcribe At Anytime.

.jpg)
.jpg)
